The annual Consumer Electronics Show (CES) was an exciting one this year. It left us with a mind-blowing glimpse into th...
Imagine a world where your lights turn on automatically as you walk in the door. Your coffee starts brewing before you e...
Data is the lifeblood of modern businesses. It fuels insights, drives decision-making, and ultimately shapes your compan...
Cyber threats are a perpetual reality for business owners. Hackers are constantly innovating. They devise new ways to ex...
Zero Trust security is rapidly transforming the cybersecurity landscape. It moves away from traditional perimeter-based ...
What are some of the key differentiators that can propel small businesses forward? They include efficiency, productivity...
Calendars, task lists, and project planning are important business tools. Many people use Microsoft’s apps to power thes...
The Internet of Things (IoT) is no longer a futuristic concept. It’s rapidly transforming industries and reshaping...
With cyber threats evolving at an alarming pace, staying ahead of the curve is crucial. It’s a must for safeguarding sen...
Have you been hearing more about email authentication lately? There is a reason for that. It’s the prevalence of phishin...
Have you ever seen a video of your favorite celebrity saying something outrageous? Then later, you find out it was compl...
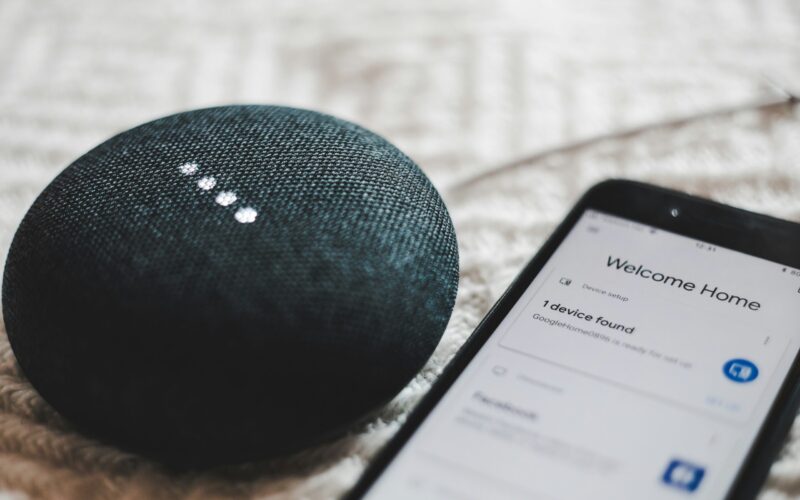
Back when you were a kid, living in a “smart home” probably sounded futuristic. Something out of Back to the Future II o...
It can be challenging to keep up with the ever-evolving cyber threat landscape. Companies need to process large amounts ...
Cloud computing has revolutionized the way businesses operate. It offers scalability, flexibility, and cost-efficiency. ...
We are living in an era dominated by digital connectivity. You can’t overstate the importance of cybersecurity. As...
QR codes are everywhere these days. You can find them on restaurant menus, flyers, and posters. They’re used both offlin...
Smart home devices are becoming more popular and convenient. But they also pose some serious security risks. Hackers can...
Google’s latest email guidelines require domain owners sending bulk messages to Gmail addresses to authenticate th...
Cybersecurity is a constantly evolving field. There are new threats, technologies, and opportunities emerging every year...
Microsoft Edge continues to redefine user experiences. This is due to Microsoft’s commitment to innovation. The latest u...